What is SPF and Why It’s Crucial to Your Business’ Cybersecurity
Key Points in The Article – What is Sender Policy Framework:
- Using the Sender Policy Framework (SPF) is essential to your cybersecurity practices.
- SPF mitigates the risk of email spoofing by helping recipient email servers authenticate the emails your business sends.
- SPF works best with DKIM and DMARC, two other email authentication methods.
If you’re a business using Office 365, enabling SPF is essential to your cybersecurity. SPF stands for Sender Policy Framework. so, what is sender policy framework? It’s a protocol that helps validate the emails you send from your domain. It prevents criminals and scammers from sending emails that appear to come from your domain – a technique known as spoofing.
Email spoofing is commonly deployed to trick individuals into providing access credentials, supplying confidential information, or downloading malware. It’s a cybersecurity concern that could result in significant financial loss, reputational damage, and legal liability. Mitigating those risks starts with configuring email authentication methods like SPF to safeguard your email messages.
What Is SPF?
Using SPF means publishing an SPF record – a TXT entry in your DNS server – that lists the IP addresses from which email servers are authorized to send emails from your domain. When you send an email, the recipient’s email server will automatically look up the SPF record, verify that your email is coming from a matching address, and allow the email through. In practice, an email that appears to come from your domain not on this list will be recognized as potentially suspicious and either automatically send your email to the recipient’s Spam inbox or be rejected entirely.
“As Gartner states, ‘Email authentication is foundational to modern cybersecurity.”
What is Sender Policy Framework and Why is it Essential?
Criminals and scammers may spoof your email address to trick your employees into handing over their personal financial information or provide access credentials or sensitive information about your business. In some cases, criminals may use spoofed emails to coax your employees into downloading malware onto your network. Or they may use spoofed emails to scam your suppliers, vendors, or customers.
Using SPF, along with other email authentication records, can substantially mitigate the risk they will be successful. Not only does the authentication process help identify criminals and scammers, but the publication of an SPF record makes the sending server a less attractive target to be spoofed.
SPF can also improve your email deliverability rates, as spam filters are less likely to denylist your domain. Without an SPF record, some email servers may flag particular IP addresses as spam generators and send all incoming emails directly to Spam. And while your emails may be completely legitimate, as most people do not regularly check their Spam folders, those emails will go unread.
What Does An SPF Record Look Like?
SPF records contain several different components. In addition to the IP address (both IPv4 and IPv6 versions as necessary), the SPF record provides the recipient’s server instructions in case of an IP address mismatch. Here’s a brief look at an SPF record if you’re hosted in Office 365:
v=spf1 include.spf.protection.outlook -all
What Does An SPF Record Look Like?
Each SPF record begins with v=spf1. The next line include.spf.protection.outlook directs the recipient server to include emails coming from Exchange Online. If you were using a third-party email system, this line would be replaced with include: with being replaced with the domain of the third-party system. If you were using dedicated Exchange Online servers, you’d list their IP addresses followed by include.spf.protection.outlook. And with an on-premises email system, you’d include the server email address(es), followed by include:.
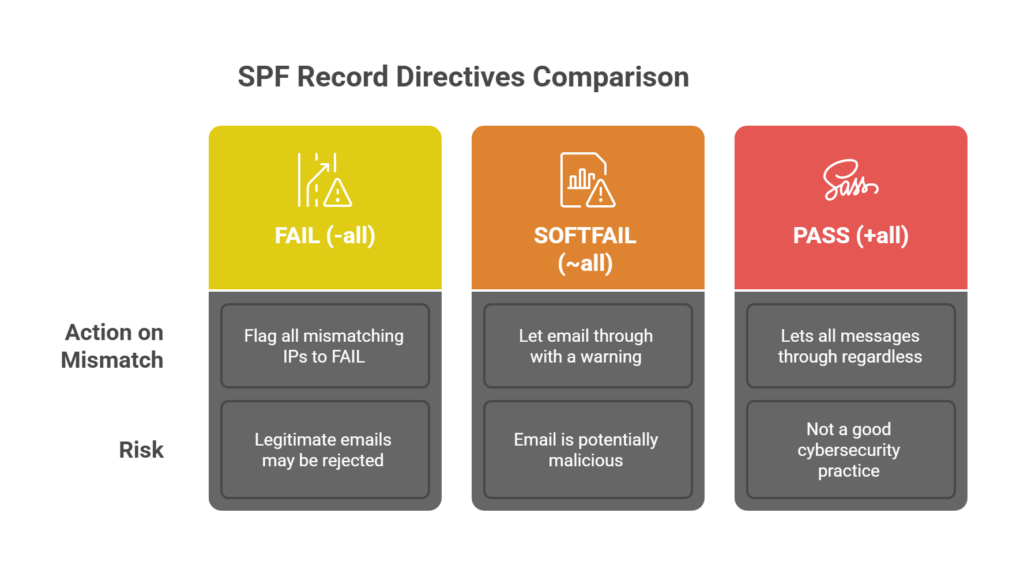
You’ll end the SPF record with your enforcement rule, which tells the recipient server what to do in case of a mismatch. The sender can tell the recipient server to flag all mismatching IP addresses to FAIL by setting an -all directive. Or the sender can use ~all to direct the recipient to let the email through with a warning that the email is potentially malicious. Doing so is referred to as a SOFTFAIL.
Using the former directive means you must accept the risk that your legitimate emails may be rejected. When mass emailing to emails from multiple domains, it may be worth sending test messages with a SOFTFAIL policy in place and assessing your results before opting for a hard fail policy. There is also an +all directive that lets all messages through regardless of the mismatch. However, using this directive would not be a good cybersecurity practice.
Office 365 already includes SPF records for Microsoft’s servers in DNS. However, some circumstances, such as operating in a hybrid environment, may require you to revise or reconfigure your SPF records. Further, it’s good practice to check to make sure they are configured correctly, especially if you’ve had to update them in the past.
Subdomains and Wildcard SPF Records
It’s also critical to note that you must add a new SPF record for each subdomain. Your subdomains do not automatically inherit their top-level domains’ SPF records. Also, attackers have attempted to send emails from nonexistent subdomains. You can create a wildcard SPF record for each domain and subdomain not covered by another DNS record you’ve created to prevent them from doing so. To create a wildcard SPF record, you would add an * to the Name field in the DNS record.
DKIM and DMARC
SPF records alone won’t prevent spoofing. But SPF is a good first step. You should also enable DKIM and DMARC email authentication protocols to provide even more protection. DKIM stands for DomainKeys Identified Mail and is an email authentication method designed to ensure that the email hasn’t been tampered with. It does this by including a digital signature to every email message, which the recipient’s system can verify in DNS.
DMARC stands for Domain-based Message, Authentication, Reporting, and Conformance and helps recipient email servers authenticate emails. It does so by adding instructions to recipient email servers about checking the From: field and ensuring that it is aligned with other domain names that have been authenticated. Further, DMARC communicates to recipient email servers that the email messages being sent are covered by SPF and/or DKIM and provides instructions to the recipient about what to do if those authentication methods fail.
Using SPF, DKIM, and DMARC in tandem provides substantially more protection against email spoofing than SPF alone. And all three can be easily configured by Office 365 users.
Understanding SPF Record Syntax and Examples
The Sender Policy Framework (SPF) is an email authentication protocol that is used to verify that a mail server is authorized to send emails on behalf of a specific domain. An SPF record is a line of text stored in a domain’s DNS that specifies which IP addresses are approved to send email for the domain. When an email is received, the mail server checks if the IP address in the email header matches the IP address in the SPF record. If the addresses don’t match, the email will fail SPF authentication.
SPF Record Mechanisms: IP Addresses, Includes, and the “All” Directive
SPF records include specific mechanisms and directives that define authorized mail servers and how to handle unauthorized emails. These mechanisms and directives include:
- ip4: This specifies IPv4 addresses authorized to send emails for the domain. For example, v=spf1 ip4:48.213.51.127 authorizes the IPv4 address 48.213.51.127.
- ip6: This specifies IPv6 addresses authorized to send emails for the domain. For example, ip6:2a05:d018:e3:8c00:bb71:dea8:8b83:851e authorizes the IPv6 address 2a05:d018:e3:8c00:bb71:dea8:8b83:851e.
- include: This directive indicates that another domain is authorized to send emails on behalf of your organization. For example, include:authorized-domain.com indicates that the domain “authorized-domain.com” can send emails on your behalf.
- all: This directive specifies the policy for handling emails from unauthorized IP addresses. There are three options:
- -all (Hard Fail): This tells the receiving server to reject emails from unauthorized IP addresses.
- ~all (Soft Fail): This marks emails from unauthorized IP addresses as potentially suspicious but still delivers them.
- +all (Pass): This bypasses all security restrictions, allowing any sender to reach the recipient’s inbox, which is considered insecure and should be avoided.
An SPF record can contain multiple mechanisms. For example:
v=spf1 ip4:48.213.51.127 ip4:31.217.43.153 ip6:2a05:d018:e3:8c00:bb71:dea8:8b83:851e include:authorized-domain.com -all
This SPF record authorizes two IPv4 addresses, one IPv6 address, includes a third-party domain, and specifies a hard fail for all other senders.
How to Check Your SPF Record
An SPF record check, or SPF validator, is a tool for determining if an SPF record is valid. These tools look up the SPF record for a domain, display any records found, and test the record for any issues. They can help identify problems that could cause mail delivery issues. You can also check your SPF record by looking at the email headers. If an SPF record passes, the message will be considered a legitimate email and reach the recipient’s inbox. If a record fails, the email will be labeled with a warning message.
Limitations of SPF and Why it’s Not a Complete Solution
While SPF is an important email authentication tool, it has limitations:
- DNS lookup limits: SPF records are limited to 10 DNS lookups, which can cause problems if the include modifier is used excessively.
- Character limits: SPF records have a 255-character limit, an inherent limitation of DNS TXT records.
- Incomplete protection: SPF does not provide end-to-end encryption or protect against all phishing attacks.
- Difficult to maintain: SPF records can be difficult to maintain, especially for organizations with complex email infrastructures.
- Breaks with forwarding: Improper email forwarding can break SPF authentication because if an email is forwarded through a server not authorized in the SPF record, the email may fail the SPF check.
- Doesn’t protect “header from” address: SPF does not protect the “header from” address that users see in their email clients, which means it can still be spoofed even if the email passes the SPF check.
- Accuracy: SPF records can become outdated if the vendors sending email on a brand’s behalf change.
- Tolerance: Email providers can use many signals to inform delivery decisions, and an SPF failure does not guarantee that a message will be blocked.
SPF, DKIM, and DMARC: A Multi-Layered Approach to Email Authentication
SPF is not a complete email security solution. It should be used in conjunction with other authentication methods like DKIM (Domain Keys Identified Mail) and DMARC (Domain-based Message Authentication, Reporting & Conformance). DMARC improves upon SPF by requiring that the information in the “from” address aligns with other information about the sender and that a message is authenticated with either SPF, DKIM, or both. DMARC also provides reporting on how messages that fail authentication should be handled.
Simplifying DMARC Implementation with DMARC Analyzer Tools
DMARC Analyzer tools help to simplify the implementation and management of DMARC policies. These tools provide features like:
- Quick setup wizards for DMARC records.
- Monitoring of DNS changes and alerts for any alterations.
- User-friendly reports and charts for easier analysis.
- Forensic reports to identify sources of malicious email.
- Coverage for unlimited users, domains, and domain groups.
- DMARC, DKIM, and SPF record checkers.
- Managed services provided by experts.
These tools help organizations to move towards DMARC authentication quickly and cost-efficiently.
Conclusion
Sender Policy Framework (SPF) is a critical email authentication method. This helps to verify that mail servers sending emails are authorized to do so on behalf of a specific domain. By creating SPF records, domain owners can specify which IP addresses are allowed to send emails for their domain, which helps prevent email spoofing and phishing attacks.
SPF also improves email deliverability and helps to maintain a good domain reputation. While SPF is a valuable tool, it is not a complete email security solution on its own and has limitations. SPF should be used in conjunction with other email authentication methods. Use methods such as DKIM and DMARC to create a more robust, multi-layered approach to email security. DMARC improves upon SPF by requiring that the information in the “from” address aligns with other information about the sender. It also provides reporting on how messages that fail authentication should be handled. Tools like DMARC analyzers can help simplify the implementation and management of DMARC policies.
FAQs: Sender Policy Framework (SPF)
1. What is a Sender Policy Framework (SPF) record?
An SPF record is a line of text stored in the DNS of a domain that specifies which IP addresses are authorized to send email for that domain.
2. How does SPF work?
The mail server checks the SPF record of the sending domain to ensure the email is legitimate when it receives an email. It compares the sending server’s IP address with the authorized addresses in the SPF record. If the source of the email is found on the list of authorized servers, the message passes the SPF check. If not, the email delivery may fail, and the email may be marked as spam or rejected.
3. Why do I need an SPF record?
To verify that inbound messages to your server originated from domains you authorized, you need an SPF record. It also helps servers you send emails to verify that your domain is authentic. SPF records reduce the chance of your emails being marked as spam.
4. What are the components of an SPF record?
An SPF record includes mechanisms such as ip4 and ip6 to specify authorized IPv4 and IPv6 addresses. It also includes the include directive to specify other domains authorized to send emails on your behalf. The all directive specifies how to handle emails from unauthorized IP addresses, using -all for a hard fail, ~all for a soft fail, or +all for bypassing security restrictions.
5. What is an SPF record check?
An SPF record check, or SPF validator, is a tool that determines whether an SPF record is valid. These tools look up the record for a domain and test for any issues that could create problems for mail delivery.
6. What are the limitations of SPF?
SPF has limitations including DNS lookup limits, character limits, and issues with email forwarding. It also does not protect the “header from” address from being spoofed. Additionally, SPF records can be challenging to maintain, especially for organizations with complex email infrastructures.
7. How does SPF relate to DKIM and DMARC?
SPF is one part of a multi-layered email authentication approach, and it works in conjunction with DKIM and DMARC. DMARC improves upon SPF by requiring that the information in the “from” address aligns with other information about the sender.
8. Can SPF completely prevent phishing attacks?
No, SPF alone cannot completely prevent phishing attacks. It is important to use a combination of email authentication methods and other security measures to protect against phishing.
Published: May 2, 2025
Need IT Support for Your Florida Business?
GiaSpace provides proactive managed IT services, cybersecurity, and local tech support across Florida — with teams in Gainesville, Fort Lauderdale, Jacksonville, and Ocala.
Managed IT Services FloridaCybersecurity Services FLGainesville IT ServicesFort Lauderdale IT Services